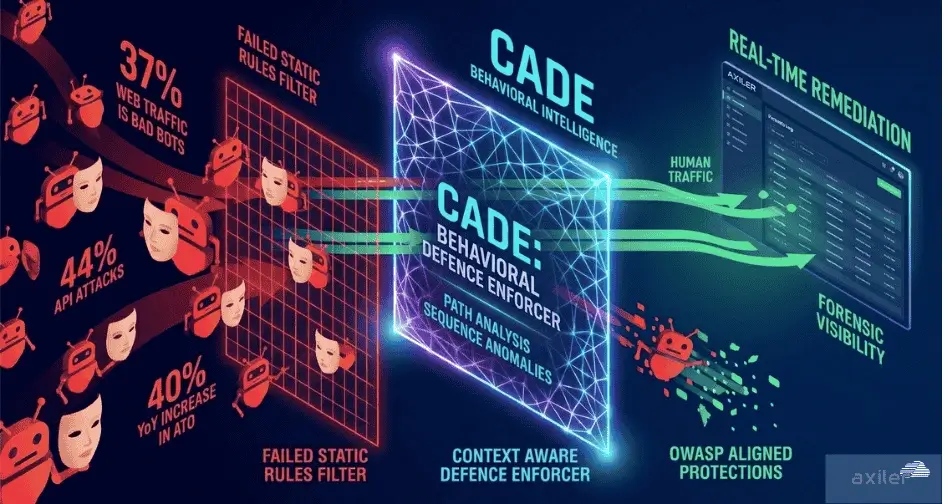
In 2024, a major threshold was crossed: automated traffic officially overtook human activity on the internet. These aren’t the simple crawlers of the early internet. Today’s bad bots are powered by AI, enhanced with real-time evasion tactics, and are increasingly responsible for API abuse, credential stuffing, scraping, and sophisticated account takeover (ATO) attacks.
This alarming rise highlights a stark truth: static, rules-based defences are no longer enough. Traditional security tools were built for predictable threats. What we face now are intelligent adversaries moving faster than human teams can respond.
The Modern Bot Landscape: A Crisis in Plain Sight
Modern bad bots are highly adaptable and purpose-built with several key trends:
• 51% of all web traffic is automated, and bad bots make up 37% of that.
• 44% of sophisticated bot attacks now target APIs, which are often underprotected.
• Account Takeover (ATO) attacks have increased by 40% year over year, with bots exploiting weak authentication systems.
• AI has lowered the barrier to entry for attackers, allowing them to launch more precise, evasive, and scalable attacks.
• Residential proxies are increasingly used to bypass IP blacklisting, making malicious traffic appear legitimate.
Among this growing bot traffic are also crawler bots, some of which are essential, such as Googlebot, Bingbot, Baiduspider, and YandexBot, which index websites for search engines. These legitimate crawlers follow standardized behaviors and respect robots.txt guidelines. However, malicious crawler bots like BlackWidow, Nutch, and Masscan are designed to imitate these good actors while scraping data, probing for vulnerabilities, or testing access controls.
What’s even more dangerous? Many of these attacks go undetected for weeks. Traditional defences are often blind to behavior-based anomalies and unable to act without human intervention. Many of these automated threats map directly to the OWASP list of top automated threats, underscoring the need for more proactive, behavior-based defences.
Why Traditional Defences Are Losing the Battle
Conventional tools work by matching incoming traffic against static rule sets or signatures. That may have worked when threats were known and consistent. But modern bots:
• Mimic human behavior to evade detection.
• Change IPs rapidly using residential proxy networks.
• Target APIs directly, bypassing frontend protections.
• Exploit business logic flaws, which rules can’t detect.
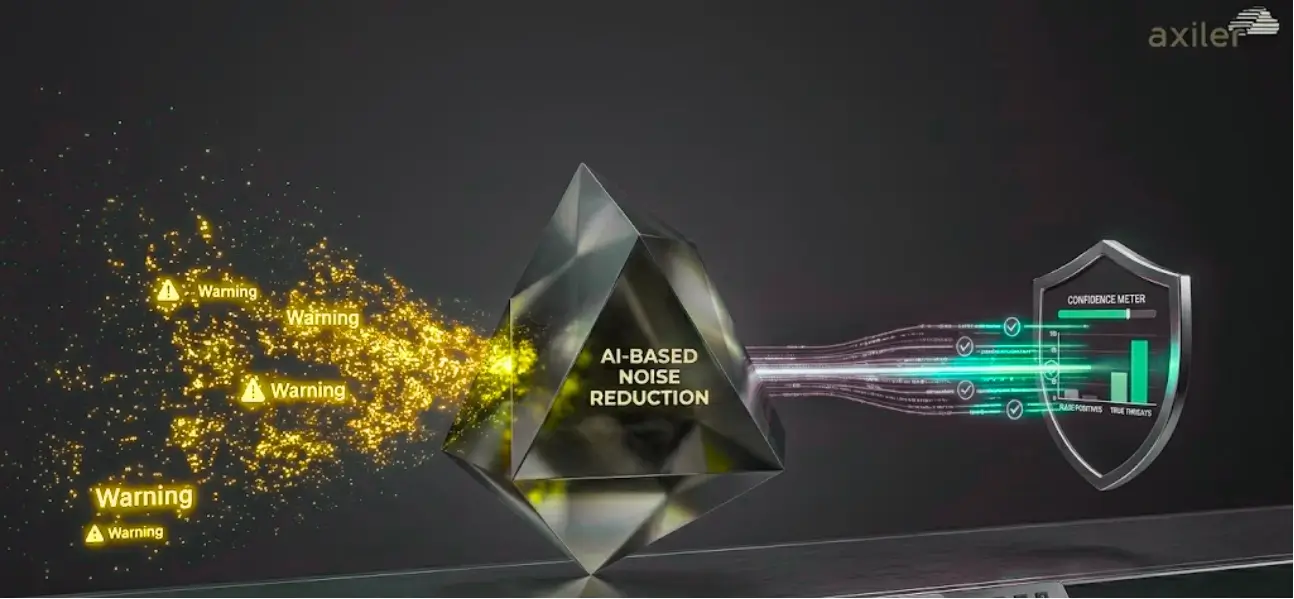
These systems also suffer from high false positives, alert fatigue, and require extensive manual tuning. Worst of all? They often stop at alerting you, without taking action.
Enter CADE: Axiler’s AI-Powered Answer to the Bot Epidemic
Axiler’s CADE (Context Aware Defence Enforcer) is a self-healing, autonomous defence system designed for cloud-native, high-velocity environments.
Here’s how CADE tackles problems highlighted above:
1. Behavioral Intelligence – CADE doesn’t rely on static rules. It analyzes real-time behavior, how bots move through your app, interact with endpoints, or abuse API calls. Legitimate crawlers follow standardized paths; malicious bots take shortcuts, break sequences, and act unpredictably. CADE sees it all.
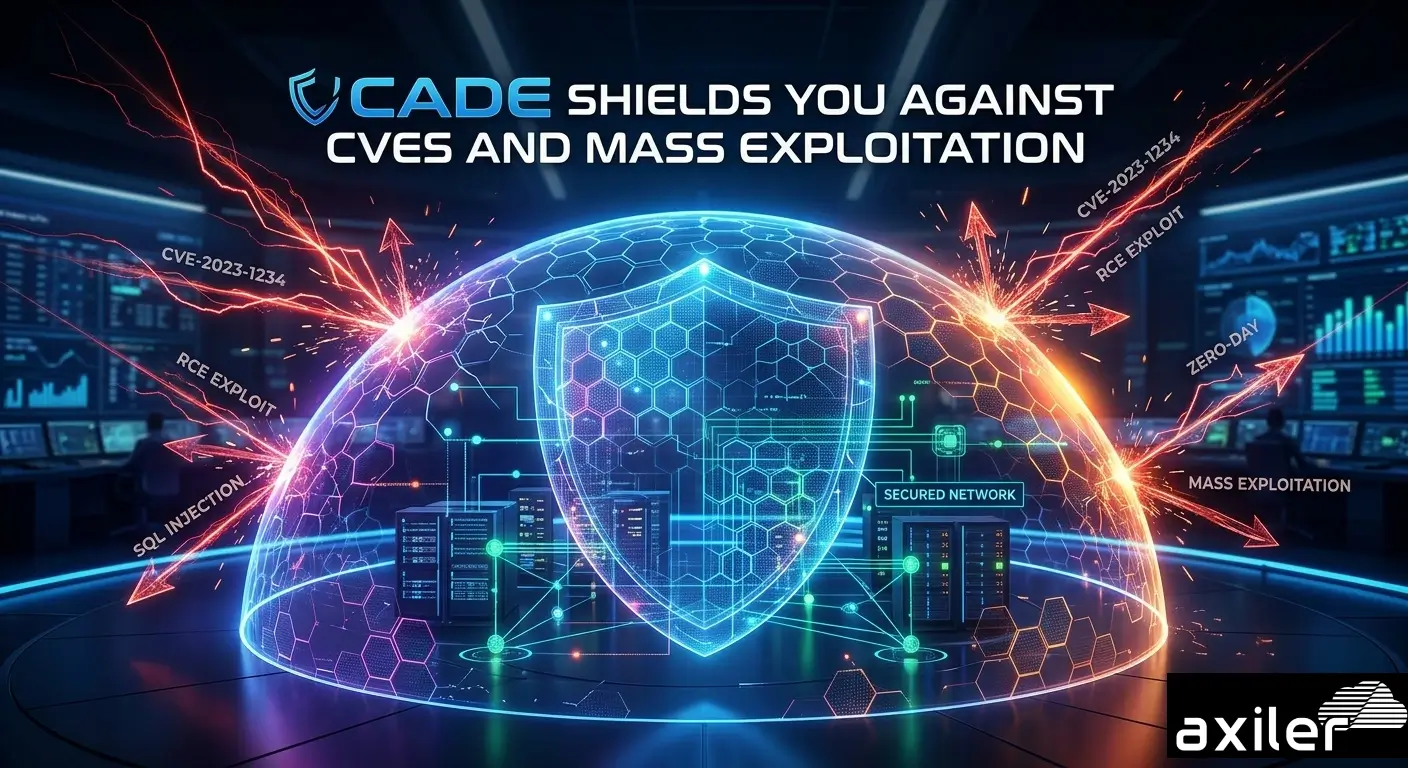
2. Real-Time Threat Remediation – CADE doesn’t just log threats, it acts. Whether it’s a zero-day exploit or a suspicious API abuse pattern, CADE neutralises attacks instantly, without needing human input.
3. Mini-SIEM Visibility Without the Complexity – CADE provides forensic-level logs in real time, giving security teams visibility into bot behavior, request origins, and anomalies, without the cost or complexity.
4. AI-Driven Rule Generation – No more babysitting your defence. CADE continuously generates and refines its own rules based on live traffic. This dramatically reduces operational overhead and increases adaptability.
5. Anomaly Forecasting – Bots don’t always attack directly. CADE uses predictive analytics to forecast future anomalies, allowing teams to prepare, not just respond.
Traditional Defences Stop at Detection, CADE Goes Further
• Detects the undetectable (bots using AI, proxies, human-like behaviour)
• Remediates instantly with no manual drag
• Predicts and prevents future attacks
• Eliminates alert fatigue with intelligent triaging
CADE is built for a world where bots evolve faster than rules. It’s the response to an industry where 90% of breaches come from misconfigurations, overlooked traffic, and delays in remediation. And unlike traditional systems, CADE’s detection capabilities are aligned with the OWASP automated threat categories, enabling smarter, rule-free protection against the most prevalent attack patterns.
Conclusion: In a World of Intelligent Bots, You Need Smarter Defence
The data is clear, automated threats are now the majority. They’re faster, smarter, and harder to detect. And they’re coming for your APIs, user accounts, and business logic.
Static rules won’t save you. Manual triage won’t scale. But CADE will.
CADE is Axiler’s answer to the next generation of automated threats. It’s not just defence, it’s autopilot-grade, predictive, and relentlessly precise.